
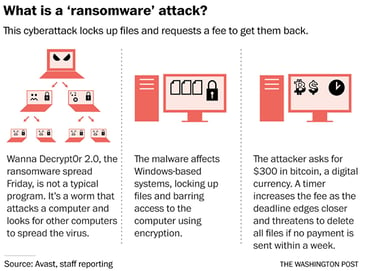
It has become increasingly common for headlines to be filled with news of recent data breaches. However one Friday in May 2017, news of a targeted type of cyber attack dominated press coverage as organizations around the world were exposed to the malicious WannaCry ransomware; also referred to as WannaCrypt, WanaCrypt0r 2.0, or Wanna Decryptor. By the close of the first day it was unleashed by hackers, it had spread to more than 74 countries, and as employees returned to work on Monday morning, many probably received similar messages as below from their IT department as they busily patched potentially affected PCs.
“We are continuing to do our work to minimize any impact on the business, but we also need your help in preventing and or minimizing the effect of such an attack.”
The WannaCry ransomware, a type of cyberattack, was designed to lock and disable Windows-based computers unless victims paid a ransom to receive a decryption key. Thankfully, a British researcher, known as “MalwareTech,” identified its kill switch and slowed down the spread of the attack. However, MalwareTech and other cybersecurity agencies globally have warned that new variants of the attack have been detected that are immune to the kill switch and warn that additional variants are expected to continue popping up as well.
According to Brad Smith, Microsoft’s president and chief legal officer, the WannaCry ransomware attack should be a wake-up call for all of us, and it should serve as a warning to reevaluate and potentially strengthen the cyber preparedness of your organization. Even though Microsoft released a security patch two months prior to this incident, many organizations remained vulnerable because their systems weren’t updated. This attack is a perfect example of why all organizations need to update their computers with the latest patches and be vigilant about notifying at-risk parties.
“Recent data breaches and WannaCry highlight the pivotal role that not only IT administrators but also all employees play in strengthening each organization’s cybersecurity,” said Shafraz Branudeen, VP, IT Operations & Infrastructure for North America, Generali Global Assistance. “A patch was available from Microsoft mid-March to address the vulnerability that WannaCry exploited but unfortunately many organizations were still affected. In some scenarios, organizations were vulnerable due to IT departments not pushing the updates to all network computers in time. Companies often need to conduct testing of Windows updates to evaluate and resolve any potential issues with critical business systems before doing a mass system updates,” explained Branudeen. “Another common situation that allowed organizations to be susceptible to WananaCry was employees deferring the installation of update,” he continued.
In addition to updating your operating systems with the latest patches, use this opportunity to analyze your organization’s policies and procedures used when cyberattacks occur. You may need to update or implement a new approach to cybersecurity to increase your immunization against any future attacks. Some popular safeguards that help mitigate risks include:
- Data encryption policies
- Employee training
- Security awareness programs
- Vulnerability assessments


.png?width=102&height=102&name=Iris-Generali-Logo-White%20(1).png)




