
When work takes your employees outside of the office, their risk of identity theft increases.
Identity thieves are becoming craftier every day. And while employees are traveling, it’s good to know some of the less obvious, but equally effective ways that thieves are gathering personal information. With less information than one might think, a thief with just a little savvy can put an identity in danger.
Boarding Passes
This small slip of paper contains a lot more information than meets the eye. While the traveler’s name and itinerary is clearly printed, housed within the barcodes – easily readable with a mobile app or a free website – is the traveler’s frequent flyer number. A shrewd criminal can use clues from the traveler’s social media profiles to answer security questions and then access their account. From there, affinity points can be cashed out and passport numbers, future itineraries, phone numbers, email addresses, mailing address, and even credit card numbers can be accessed. With this information, the traveler’s financial accounts are then accessible by the identity thief, including company credit cards linked to the traveler’s profile.
Travelers react to learning their boarding pass can be used to access personally identifiable information.
We always recommend business travelers shred boarding passes after use (or use mobile versions when possible), make security questions especially challenging, increase privacy settings on social media sites, and unlink credit cards from frequent flyer accounts to reduce risk. Additionally, a comprehensive identity monitoring program, like ours, should have the ability to monitor even affinity account and passports for suspicious activities, and alert you when they arise. Being notified of such fraudulent activity early on allows consumers to lessen the potential the fall out of the fraud.
ATMs
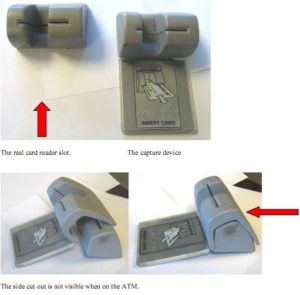
Dubious restaurants and vendors, sometimes unknowingly compromised ones, have been the more well-known perpetrators of a common identity theft technique using card skimming machines that save card data when being swiped for a purchase. Increasingly, these are becoming more nondescript. Card skimmers can be disguised as promotional fixtures on ATMs or can fit over a machine’s card slot to read account numbers and steal PINs. According to FICO Card Alert Service, ATM fraud increased six-fold in 2015 from the previous year. See this example from Krebs on Security:
 Avoid getting skimmed and scammed by carefully inspecting the ATM before using it. Look for any additional structure on or around the key reader or attached overhead (these can contain cameras that capture your card number and watch you enter the PIN). Cover your PIN with your hand and use ATMs located in well-lit areas attached to a bank. Check bank accounts regularly to monitor for suspicious charges. Use an identity monitoring program to ensure stolen account numbers aren’t being circulated on the black web and to monitor credit reports for significant changes in credit profiles.
Avoid getting skimmed and scammed by carefully inspecting the ATM before using it. Look for any additional structure on or around the key reader or attached overhead (these can contain cameras that capture your card number and watch you enter the PIN). Cover your PIN with your hand and use ATMs located in well-lit areas attached to a bank. Check bank accounts regularly to monitor for suspicious charges. Use an identity monitoring program to ensure stolen account numbers aren’t being circulated on the black web and to monitor credit reports for significant changes in credit profiles.
Public Wi-Fi
“Is there Wi-Fi?” – the seminal business traveler question. You hear it in restaurants, airports, hotel lobbies, and – throughout large cities – even in taxi cabs. Wi-Fi is the lifeblood of business travelers on the road who need access to emails, calendars, and corporate servers. However, unsecured public Wi-Fi hotspots can also be a useful tool for identity thieves.
Private Wi-Fi at home or at the office generally has a number of protocols in place that make browsing, entering passwords, and sending sensitive information relatively safe. This isn’t always the case for public Wi-Fi. A study by Private Wi-Fi and the Identity Theft Resource Center revealed that even though 76% of Wi-Fi users knew the risks of public Wi-Fi, 71% still checked email, 13% accessed business documents, and another 13% entered in their credit card number. Eleven percent even accessed their bank info!
Some common public Wi-Fi cons by identity thieves include the Honeypot Attack, the Evil Twin, Packet Sniffers, and ARP Spoofing. But, these funny names are no laughing matter. If the transmitted data is sensitive to the business, it could be the gateway for an identity thief to breach a company.
Keep your traveling employees safe by providing a Virtual Private Network (VPN) that will encrypt data – even outside the office. Additionally, the online data protection (ODP) software offered with our identity protection services alerts users to unsecured websites and scrambles keystrokes so they’re untraceable by malware surreptitiously installed on the device.
Mitigate Risk with a Monitoring Program and Data Protection Suite
While education is the first step in making sure that your traveling employees minimize their risk, having a monitoring program that continuously scans the internet for suspicious activity can be an important tool for early detection of identity theft, minimizing the negative outcomes for the employee and reducing the chances of compromising company data. To learn more about our comprehensive identity protection, request a demo.
You can also read the "Protecting Employees’ Identities" series introduction article.


.png?width=102&height=102&name=Iris-Generali-Logo-White%20(1).png)




